Vulnerability management, risk assessment, and application security form the operational backbone of a modern cybersecurity program. This video outlines a services stack focused on identifying weaknesses (scanning, pentesting), quantifying risk, and continuously managing the attack surface. The scope spans infrastructure, applications, wireless, and cloud environments, with an emphasis on measurable risk reduction rather than one-off audits.
At the application layer, the focus shifts to secure development and runtime protection: code reviews, web and API security testing, and integration of security into DevSecOps pipelines. Supporting practices such as SAST/DAST and Software Composition Analysis (SCA) address both custom code and third-party dependencies. Overall, the approach is continuous and layered — combining vulnerability discovery, risk prioritization, and remediation across the full stack.
FAQ
Contact Us
- Tell us more about your business and what you need from automation and business software.
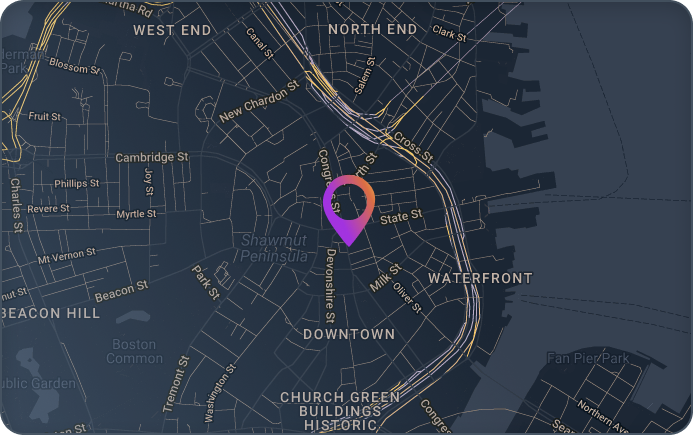
- One Financial Center
16th Floor
Boston, MA 02111 - Request a Quote: +1 (833) 695-0811